WordPress
7-Step Website Security Checklist for Enterprise WordPress Teams
José Debuchy
February 17, 2026 | 3 min to read
Protecting enterprise WordPress sites from cyber threats quickly becomes overwhelming as teams juggle complex infrastructure, plugin ecosystems, and a growing list of user accounts. One missed update or a forgotten permission setting can open the door to serious security breaches and downtime. You need a proven approach that tackles real-world risks without slowing down your organization.
This list breaks down the most effective strategies trusted by global enterprises for hardening WordPress security. You will discover clear steps that go beyond theory, covering actionable measures for audits, authentication, patching, and more. Get ready to strengthen every layer of your WordPress environment with practical techniques you can implement right away.
Quick Summary
| Takeaway | Explanation |
|---|---|
| 1. Conduct Regular Security Audits | Perform comprehensive audits quarterly to identify and fix vulnerabilities before exploitation. |
| 2. Implement Strong Authentication Practices | Enforce two-factor authentication and set granular user roles to enhance security. |
| 3. Automate Patch Management | Regularly apply automated updates to keep your site secure against known threats. |
| 4. Utilize Secure Hosting Solutions | Choose hosting with advanced security features like DDoS mitigation and SSL encryption. |
| 5. Monitor User Activity Diligently | Maintain detailed logs of user actions to provide insights for audits and security investigations. |
1. Conduct Regular Security Audits and Penetration Testing
Enterprise WordPress teams must implement systematic security evaluations to protect their digital infrastructure from emerging cyber threats. Regular security audits provide a comprehensive approach to identifying and mitigating potential vulnerabilities before they can be exploited.
A comprehensive security audit goes beyond basic scanning. It involves a multilayered examination of your WordPress environment that includes:
- Comprehensive plugin version checks
- Thorough user permission assessments
- Server configuration vulnerability scanning
- Identification of potential cross-site scripting (XSS) risks
- Detection of potential cross-site request forgery (CSRF) attack vectors
Penetration testing takes this process further by simulating real-world cyberattack scenarios. Ethical hackers attempt to exploit your system’s weaknesses using sophisticated techniques that mimic actual threat actors. This proactive approach allows your team to:
- Discover hidden security gaps
- Test incident response protocols
- Validate existing security measures
- Prioritize remediation efforts
Security audits are not a one-time event but a continuous process of assessment and improvement.
Recommended Frequency: Conduct comprehensive security audits quarterly and perform penetration testing at least twice annually. Smaller, incremental checks should happen monthly to ensure ongoing protection.
Pro tip: Automate initial vulnerability scans but always include manual expert review to catch nuanced security risks that automated tools might miss.
2. Enforce Strong Authentication and Role Management
Enterprise WordPress sites demand robust authentication mechanisms that go beyond basic username and password protection. Two-factor authentication represents a critical defense against unauthorized access and potential security breaches.
Role management is a fundamental strategy for minimizing potential attack surfaces within your WordPress ecosystem. By implementing strategic user permission controls, enterprises can significantly reduce the risk of internal and external security threats.
Key authentication and role management practices include:
- Implementing mandatory two-factor authentication
- Creating granular user role permissions
- Enforcing complex password requirements
- Limiting administrative access to essential personnel
- Regularly auditing user privileges and access levels
For enterprise WordPress environments, role-based access control provides a structured approach to managing user permissions. This approach follows the principle of least privilege by ensuring users have only the minimum access required to perform their specific job functions.
Enterprise-grade security requires a dynamic and proactive approach to user authentication and access management.
Single Sign-On (SSO) integration offers additional layers of security by centralizing authentication through trusted identity providers. This strategy reduces password fatigue while maintaining strict access controls.
Pro tip: Implement quarterly user access reviews to automatically identify and revoke unnecessary or outdated user permissions across your WordPress infrastructure.
3. Implement Automated Security Updates and Patch Management
Enterprise WordPress environments require a systematic approach to managing security patches and updates. Patch management strategies are critical for maintaining a secure and resilient digital infrastructure.
Effective automated update management goes beyond simple plugin refreshes. It involves a comprehensive process of identifying vulnerabilities, prioritizing risks, and deploying patches with minimal operational disruption.
Key components of a robust patch management strategy include:
- Creating a complete inventory of all WordPress components
- Establishing clear patch deployment workflows
- Implementing risk-based prioritization protocols
- Developing staged testing environments
- Automating vulnerability monitoring
- Verifying patch compatibility before full deployment
The National Institute of Standards and Technology recommends a structured approach to patch management that aligns security protocols with broader business objectives. This means treating security updates not as isolated events but as part of a comprehensive risk management strategy.
Automated patch management transforms reactive security into a proactive defense mechanism.
For enterprise WordPress sites, this approach minimizes potential attack surfaces by ensuring that core systems themes and plugins are consistently updated with the latest security protections.
Pro tip: Develop a dedicated staging environment that mirrors your production site to test patches and updates before deploying them to live systems.
4. Secure Hosting, Backups, and Content Delivery Networks
Enterprise WordPress environments require robust infrastructure that goes beyond basic website hosting. Secure WordPress hosting represents a comprehensive approach to protecting your digital assets through multiple layers of defense.
Hosting security encompasses several critical components that work together to safeguard your digital platform:
- Real-time malware scanning
- Enterprise-grade firewall protection
- Distributed denial of service (DDoS) mitigation
- Continuous plugin and theme monitoring
- Automated offsite daily backups
- SSL encryption across all network communications
Content Delivery Networks (CDNs) play a crucial role in both performance and security. Network edge protection provides an additional shield by filtering malicious traffic before it reaches your origin server. This distributed approach means potential threats are intercepted and neutralized far from your primary infrastructure.
Secure hosting is not just a technical requirement it is a strategic business imperative.
The symbiotic relationship between premium hosting providers and CDNs creates a robust security ecosystem. By combining server hardening advanced firewall technologies and continuous updates these systems provide comprehensive protection for global WordPress deployments.
Pro tip: Select a hosting provider that offers automated daily backups with one-click disaster recovery and ensures your backup files are stored in geographically separate data centers.
5. Deploy Web Application Firewalls and Advanced Threat Protection
Enterprise WordPress sites require sophisticated defense mechanisms that go beyond traditional security approaches. Web application firewalls represent a critical line of defense against increasingly complex cyber threats.
Advanced threat protection involves implementing multilayered security strategies that dynamically adapt to emerging risks. These systems do more than simply block known attack vectors they anticipate and neutralize potential vulnerabilities before they can be exploited.
Key components of comprehensive web application firewall protection include:
- Real-time threat detection
- Advanced heuristic analysis
- Blocking SQL injection attempts
- Preventing cross-site scripting (XSS)
- Intercepting remote code execution attacks
- Analyzing GET POST and COOKIE data
- Zero latency security processing
The most effective web application firewalls operate in two critical modes: learning and active protection. In learning mode these systems gather intelligence about normal traffic patterns while in protection mode they actively block malicious requests with surgical precision.
Web application firewalls transform passive defense into an intelligent proactive security ecosystem.
By implementing sophisticated threat detection mechanisms enterprise teams can significantly reduce their exposure to potential cyberattacks while maintaining optimal website performance.
Pro tip: Configure your web application firewall to maintain separate learning and blocking configurations allowing gradual refinement of threat detection rules without risking false positive disruptions.
6. Monitor User Activity and Log Access for Audit Trails
Enterprise WordPress environments require comprehensive visibility into user interactions and system changes. Audit trail logging provides a forensic-level mechanism for tracking and understanding user activities across complex digital platforms.
Effective user activity monitoring goes beyond simple login tracking. It involves capturing granular details that help enterprises maintain security accountability and regulatory compliance.
Key components of robust audit trail logging include:
- Real-time tracking of user actions
- Detailed login attempt records
- Content modification timestamps
- User role change notifications
- Plugin and theme update logs
- Precise IP address documentation
- Exact field-level change tracking
Comprehensive Logging enables enterprises to reconstruct digital events with precision. By maintaining detailed records organizations can quickly investigate suspicious activities identify potential security breaches and ensure user accountability.
Audit trails transform passive record-keeping into an active security intelligence system.
Modern WordPress security strategies recognize that logging is not just documentation it is a critical defense mechanism. These detailed records support forensic analysis incident response and compliance with regulations like GDPR and PCI DSS.
Pro tip: Configure your audit logging to automatically archive and encrypt log files offsite ensuring a tamper-resistant record of all system activities.
7. Train Marketing Teams on Secure Publishing Workflows
Enterprise WordPress security extends far beyond technical configurations and requires comprehensive team education. Secure publishing workflows transform marketing teams from potential security vulnerabilities into proactive digital defenders.
Training programs must go beyond basic platform knowledge and focus on building a security-first culture within marketing departments. This approach ensures that every team member understands their role in maintaining organizational digital safety.
Key elements of effective security training include:
- Understanding content publishing guardrails
- Recognizing potential security risks
- Learning platform-specific compliance protocols
- Implementing consistent branding standards
- Mastering emergency response procedures
- Developing proactive site monitoring skills
Interactive Workshops provide the most effective learning environment. These sessions allow marketing professionals to practice secure workflows through realistic scenarios that simulate potential security challenges.
Security training is not a one-time event but an ongoing organizational commitment.
Successful enterprise WordPress teams integrate continuous learning into their operational model. This means regular refresher courses performance optimization strategies and strategic partnerships with platform experts.
Pro tip: Create quarterly security simulation exercises that test your marketing team’s ability to identify and respond to potential publishing risks in a controlled environment.
Below is a comprehensive table summarizing the key strategies and best practices for maintaining robust security for enterprise WordPress environments as discussed in the article.
| Security Practice | Description | Primary Benefit |
|---|---|---|
| Regular Security Audits and Penetration Testing | Conduct systematic evaluations to identify and mitigate vulnerabilities and simulate real-world attack scenarios. | Proactively addresses and closes security gaps. |
| Strong Authentication and Role Management | Implement two-factor authentication, enforce complex passwords, and manage user permissions strategically. | Minimizes unauthorized access and streamlines role-specific access. |
| Automated Security Updates and Patching | Deploy scheduled updates and apply patches while testing compatibility in staging environments. | Ensures up-to-date protection with reduced operational risks. |
| Secure Hosting and Backup Solutions | Utilize hosting with security features, daily offsite backups, and content delivery networks (CDNs). | Safeguards data integrity and enhances site reliability. |
| Web Application Firewalls and Threat Detection | Implement adaptive firewalls to monitor, block, and mitigate various cyberattack attempts. | Provides real-time defense and anticipates emerging threats. |
| User Activity Monitoring and Audit Trails | Capture detailed user interaction logs for enhanced transparency and compliance. | Facilitates forensic analysis and regulatory adherence. |
| Marketing Team Security Training | Educate marketing teams on secure publishing and organization-wide safety protocols. | Promotes a culture of security awareness and proactive risk management. |
Secure Your Enterprise WordPress Platform with 40Q
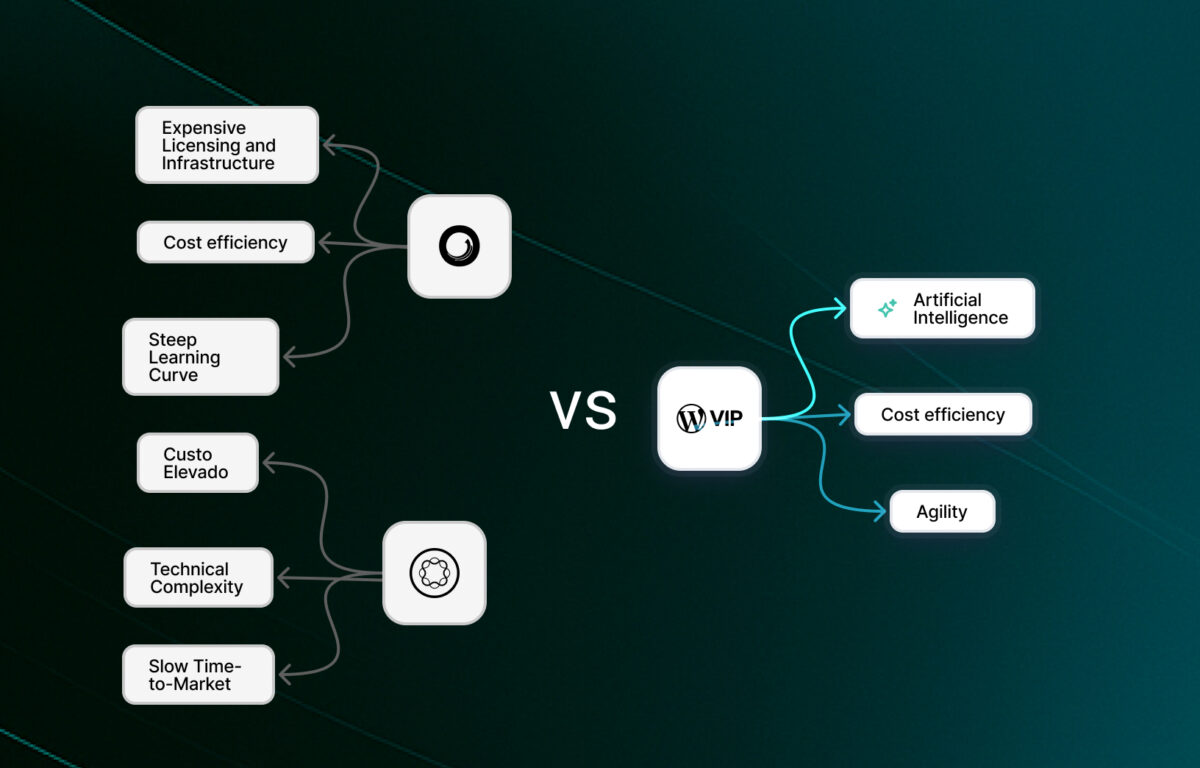
Enterprise teams face critical challenges in maintaining robust WordPress security while empowering marketing with autonomy and speed. This 7-step checklist highlights essential strategies like regular audits, strong authentication, automated patch management, and comprehensive threat protection that many organizations struggle to implement effectively without developer bottlenecks or compliance risks. 40Q addresses these pain points by delivering enterprise-grade WordPress solutions built for high-traffic, content-heavy organizations that demand both security and marketing agility.
Unlock the power of secure and scalable WordPress with 40Q. Our proprietary FAS Block System™ enables marketing teams to launch campaigns and localized content swiftly while ensuring IT retains control over security, performance, and governance. Don’t wait to protect your brand and streamline workflows. Explore how our partnership with WordPress VIP can transform your enterprise CMS environment today by visiting 40Q and learn more about our focus on enterprise security. Take control now and safeguard your WordPress site with speed and reliability.
Frequently Asked Questions
How often should I conduct security audits for my Enterprise WordPress site?
You should conduct comprehensive security audits quarterly and perform penetration testing at least twice a year. Additionally, small, incremental checks should be performed monthly to ensure ongoing protection.
What measures can I take to strengthen authentication for my WordPress team?
Implement mandatory two-factor authentication and create granular user role permissions to enhance security. Regularly audit user privileges, limiting administrative access to essential personnel to further reduce risks.
What is a patch management strategy and why is it important?
A patch management strategy involves systematically managing security patches and updates for your WordPress environment. This helps maintain a secure infrastructure by ensuring that you identify vulnerabilities and deploy patches effectively, minimizing operational disruption.
How can we secure our hosting and backup systems?
Choose a hosting provider that offers real-time malware scanning, enterprise-grade firewall protection, and automated offsite daily backups. This layered approach helps safeguard your WordPress site against various threats while ensuring data is recoverable in case of an incident.
What role does user activity logging play in website security?
User activity logging captures detailed records of user actions and system changes, providing visibility into potential security breaches. Configure your audit logging to automatically archive logs offsite to maintain a tamper-resistant record of all activities.
Why is training marketing teams important for website security?
Training marketing teams on secure publishing workflows helps foster a security-first culture within your organization. Regular workshops and simulation exercises enable team members to recognize potential security risks and respond effectively during actual incidents.
Recommended
- How to Secure WordPress for Enterprise-Grade Protection – 40Q
- Role of Security in Website Development: Impact on Enterprise WordPress Platforms – 40Q
- WordPress Security is better than you think – 40Q
- Enterprise Website Best Practices for Rapid Growth – 40Q
- Hébergement de site web via Amazon | Yelido
Nov 7, 2024
WordPress
5 Things You Didn’t Know WordPress Could Do
Jan 17, 2026
WordPress
7 Essential Tools for Website Performance Monitoring List
May 14, 2025
WordPress