WordPress
Role of Security in Website Development: Impact on Enterprise WordPress Platforms
José Debuchy
February 2, 2026 | 3 min to read
High-traffic WordPress environments at enterprise scale attract sophisticated cyber threats that can disrupt operations and compromise valuable data. As digital platforms grow and regulatory demands intensify, CTOs and IT Directors must tackle the challenge of protecting confidential information while keeping services available and compliant. This article breaks down website security essentials and practical strategies to help large organizations safeguard WordPress sites, balance developer autonomy, and maintain resilience against evolving attacks.
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive Security Strategy | Enterprises must implement a multifaceted approach to website security that includes advanced network protection, user authentication, and continuous vulnerability monitoring. |
| Addressing Evolving Threats | Recognizing the complexity of modern cyber threats, enterprises should adopt proactive and adaptive security measures to counteract multiple potential attack vectors. |
| Compliance and Governance | Businesses must establish robust governance frameworks that ensure compliance with data protection regulations and facilitate effective data management. |
| Balancing Security and Innovation | Organizations need to create governance structures that enable developer autonomy while maintaining stringent security and compliance protocols. |
Defining Website Security for Enterprises
Website security represents a comprehensive digital defense strategy that enterprises deploy to protect their online infrastructure from sophisticated cyber threats. At its core, website security involves implementing multifaceted technological and procedural safeguards designed to prevent unauthorized access, data breaches, and malicious attacks across web platforms.
For enterprises, website security encompasses a complex range of protective measures, including:
- Advanced network protection protocols
- User authentication systems
- Data encryption technologies
- Continuous vulnerability monitoring
- Robust access control mechanisms
Enterprise web security strategies must address multiple potential attack vectors, recognizing that modern cybersecurity challenges extend far beyond traditional perimeter defenses. Sophisticated threat actors continuously develop new methods to exploit system vulnerabilities, making proactive and adaptive security approaches essential.
The primary objectives of enterprise website security include maintaining confidentiality, integrity, and availability of digital assets. This means preventing unauthorized data access, ensuring information remains unaltered during transmission, and guaranteeing that critical web services remain operational under various potential threat scenarios.
Website security is not a one-time implementation but an ongoing, dynamic process of assessment, adaptation, and improvement.
Pro tip: Implement a continuous security assessment protocol that regularly tests and updates your website’s defensive capabilities against emerging cyber threats.
Types of Threats Facing Enterprise WordPress Sites
Enterprise WordPress platforms face a sophisticated and evolving landscape of cybersecurity threats that demand comprehensive and adaptive defense strategies. WordPress security challenges have become increasingly complex, with attackers developing more nuanced methods to exploit potential vulnerabilities across web infrastructures.
The most prevalent types of cyber threats targeting enterprise WordPress sites include:
- Cross-Site Scripting (XSS) attacks
- Cross-Site Request Forgery (CSRF) vulnerabilities
- SQL Injection exploits
- Credential stuffing attempts
- Brute force authentication attacks
- Zero-day plugin and theme vulnerabilities
- Malware infection strategies
Cybercriminals leverage multiple attack vectors to compromise WordPress sites, with XSS being particularly dangerous. These attacks enable malicious actors to inject harmful scripts into web pages, potentially hijacking user sessions, stealing sensitive data, and compromising entire digital ecosystems.

Here’s a comparison of common enterprise web threats and their potential business impact:
| Threat Type | Attack Method | Business Impact |
|---|---|---|
| Cross-Site Scripting (XSS) | Script injection | Data theft and session hijacking |
| SQL Injection | Malicious queries | Database manipulation or breach |
| Brute Force Attack | Repeated logins | Account compromise risk |
| Zero-Day Vulnerability | Unknown exploits | Service disruption or defacement |
| Malware Infection | Malicious code upload | Website blacklist and reputation loss |
Sophisticated threat actors continuously evolve their techniques, making proactive security monitoring and rapid response critical for enterprise WordPress platforms.
Pro tip: Implement automated vulnerability scanning and patch management systems that continuously monitor and update WordPress core, plugins, and themes against emerging security threats.
Core Security Controls and Best Practices
Enterprise WordPress security demands a comprehensive, multi-layered approach that goes beyond basic protection mechanisms. WordPress security hardening requires strategic implementation of advanced controls that address potential vulnerabilities across technical and administrative domains.
Key security controls for enterprise WordPress platforms include:
- Two-Factor Authentication (2FA) implementation
- Role-Based Access Control (RBAC)
- Web Application Firewall (WAF) deployment
- Regular security patch management
- Comprehensive user permission auditing
- Advanced endpoint protection systems
- Continuous vulnerability scanning
Authentication represents a critical first line of defense, with enterprises increasingly adopting sophisticated mechanisms like Single Sign-On (SSO) and multi-factor authentication protocols. These approaches significantly reduce the risk of unauthorized access by creating multiple verification checkpoints that potential attackers must navigate.
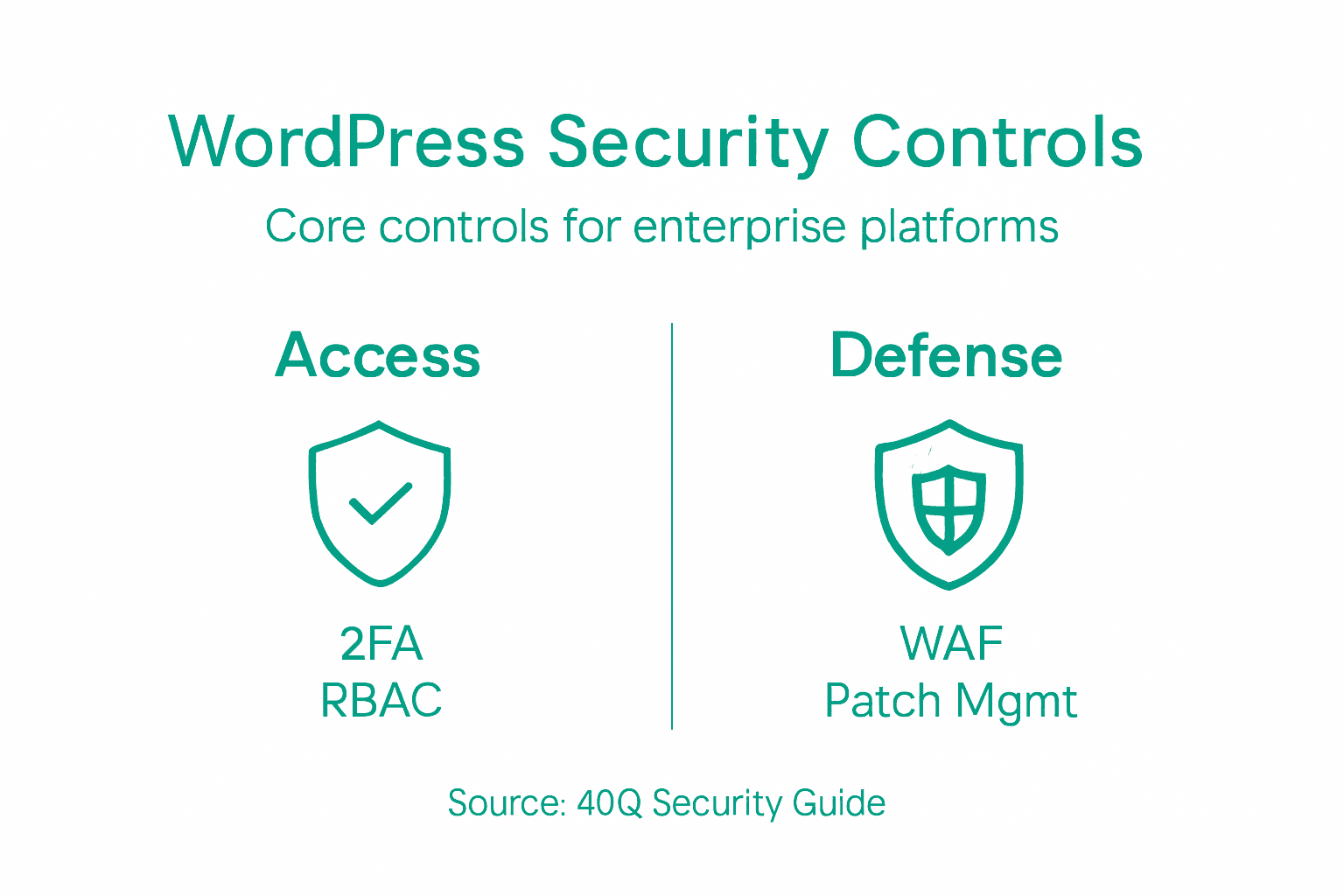
Below is a summary of core WordPress security controls and their primary functions:
| Control | Main Function | Operational Benefit |
|---|---|---|
| Two-Factor Authentication | Additional login verification | Reduces unauthorized access |
| Web Application Firewall | Blocks web-based attacks | Minimizes threat exposure |
| Patch Management | Updates software vulnerabilities | Prevents exploit attempts |
| Role-Based Access Control | Restricts user permissions | Limits internal risk |
Security is not a destination but a continuous journey of assessment, adaptation, and improvement.
Pro tip: Implement a quarterly security review process that systematically evaluates and updates access controls, patches all software components, and conducts comprehensive vulnerability assessments.
Compliance, Data Protection, and Governance Needs
Enterprise WordPress platforms must navigate a complex landscape of regulatory requirements and data protection standards that demand sophisticated governance frameworks. Compliance is no longer a peripheral consideration but a fundamental architectural requirement for digital platforms handling sensitive information.
Key compliance and governance considerations include:
- Data privacy regulation alignment
- Information security frameworks
- Audit trail documentation
- Access control governance
- Continuous compliance monitoring
- Incident response protocols
- Data retention and deletion policies
- Cross-border data transfer regulations
Organizations must implement comprehensive data governance strategies that provide granular control mechanisms while maintaining operational flexibility. This involves creating robust policies that define user roles, establish clear accountability protocols, and ensure systematic tracking of all digital interactions within the WordPress environment.
Effective governance transforms compliance from a bureaucratic burden into a strategic organizational advantage.
Pro tip: Develop a centralized compliance dashboard that provides real-time visibility into access controls, data flows, and potential regulatory risks across your WordPress infrastructure.
Balancing Speed, Autonomy, and Security at Scale
Enterprise WordPress platforms require a nuanced approach to managing technological complexity while maintaining robust security postures. Developer autonomy with security guardrails represents a critical strategy for organizations seeking to optimize their digital infrastructure.
Key considerations for achieving this delicate balance include:
- Implementing self-service development platforms
- Creating automated compliance checkpoints
- Establishing clear ownership boundaries
- Developing granular access control mechanisms
- Designing flexible yet secure workflow architectures
- Integrating continuous monitoring systems
- Enforcing standardized security protocols
Successful enterprises treat their WordPress infrastructure as a governed ecosystem, not merely a content management system. This approach requires sophisticated operational discipline that allows teams to innovate rapidly while maintaining strict security and compliance standards. Advanced organizations create integrated toolchains that streamline workflows, reduce onboarding friction, and provide real-time visibility into potential risks.
Speed without security is dangerous; security without innovation is restrictive.
Pro tip: Design a flexible governance framework that uses automated guardrails to enforce security policies while providing developers meaningful autonomy to create and iterate quickly.
Secure Your Enterprise WordPress Platform Without Slowing Down Your Team
The article highlights the critical challenge enterprises face in balancing robust website security with the need for speed, autonomy, and scalability on WordPress platforms. Complex threats like XSS attacks and zero-day vulnerabilities demand a proactive, multilayered defense strategy while marketing teams need freedom to launch campaigns quickly without being bottlenecked by developers. If you want to overcome these pain points—eliminate constant developer dependency, maintain stringent security controls, and empower your marketing team—you need a solution specifically designed for high-traffic, content-heavy enterprises.
At 40Q, we build enterprise-grade WordPress platforms that combine advanced security best practices with AI-assisted content workflows and marketing autonomy. Our proprietary FAS Block System™ enables your marketing team to quickly create landing pages and localized content while your IT team retains full control over performance, governance, and compliance. Experience the balance between innovation and security you need to protect your digital assets and accelerate speed to market. Learn how our expertise in enterprise WordPress platforms helps organizations like yours secure their websites without slowing down growth.
Start your journey to a faster, safer WordPress site now by visiting 40Q and discover how to empower your teams while safeguarding your enterprise.
Frequently Asked Questions
What are the primary objectives of website security for enterprise WordPress platforms?
Website security aims to maintain confidentiality, integrity, and availability of digital assets, preventing unauthorized access, ensuring unaltered information during transmission, and keeping critical web services operational.
What types of threats do enterprise WordPress sites commonly face?
Common threats include Cross-Site Scripting (XSS), SQL Injection attacks, Brute Force authentication attempts, and malware infections, among others, all targeting potential vulnerabilities in web infrastructure.
What are some essential security controls for enterprise WordPress platforms?
Key security controls include Two-Factor Authentication (2FA), Role-Based Access Control (RBAC), Web Application Firewalls (WAF), regular security patch management, and continuous vulnerability scanning.
How can enterprises ensure compliance and data protection in their WordPress environments?
Enterprises should implement comprehensive data governance strategies, aligning with data privacy regulations, maintaining audit trails, and establishing continuous compliance monitoring to safeguard sensitive information.
Recommended
Feb 8, 2026
WordPress
Lead Generation Process Guide for Enterprise WordPress Success

Apr 11, 2026
WordPress
How to build a marketing autonomy workflow in WordPress
Mar 10, 2026
WordPress